Are OpenClaw models Trojan Horses? The raw truth about AI Agents that "Automate" your life
Are OpenClaw AI agents Trojan horses? Independent security analysis reveals critical risks: 85% credential theft, zero compliance certs, no data guarantees. Read the raw truth. OpenClaw and QClaw promise to automate your digital life—but at what cost? With no SOC 2, GDPR certifications, or third-party audits, these "free" AI agents operate with your privileges and zero accountability. Independent testing shows 85.71% success rate in credential extraction. If the service is free, you are the product.

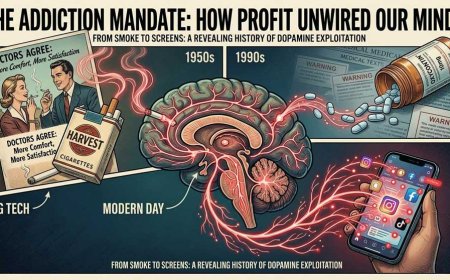
"If the service is free, you are the product."
Today, this phrase no longer applies only to social networks. It applies to the AI agents we voluntarily install, to which we grant the keys to our digital home, and which operate on our behalf without any third-party guarantor.
The Illusion of Control: "I Installed It, Therefore I Control It"
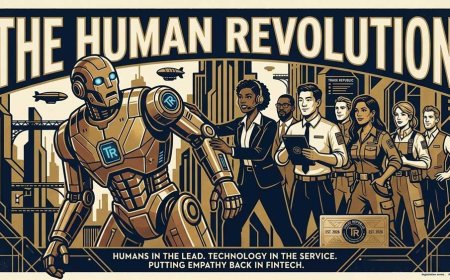
OpenClaw (Shartify Trust Rank: 1.3) and now QClaw (Tencent's version) present themselves as open-source or "community-driven" tools. The user downloads them, configures them, runs them locally or on a personal cloud. The narrative is reassuring: "You decide. You control. You automate".
The technical reality is the opposite.
To function, an AI agent must operate with extended privileges: file system access, shell command execution, environment variable reading, interaction with external APIs, browser session management, integration with CRMs, email, cloud storage. This isn't a bug. It's a feature.
But granting sudo, OAuth tokens, or API keys to an uncertified process isn't control.
It's delegation of digital sovereignty.
And when you delegate, you no longer govern. You host.
The modern Trojan Horse: it doesn't enter by force. It enters with your permission
A contemporary trojan horse doesn't need zero-day exploits or sophisticated phishing. You install it yourself. You provide the credentials yourself. You tell it to act on your behalf. And it learns, observes, records, exports.
The difference between an AI agent and traditional malware is only declared intent.
But intent can change with an update. With a policy shift. With a corporate decision.
And here's the raw data: no third-party entity certifies OpenClaw or QClaw. No SOC 2. No ISO 27001. No DPA (Data Processing Agreement). No published independent audit.
Just code, promises, and a business model that doesn't explicitly declare how it will monetize the access you grant.
The data doesn't lie: real vulnerabilities, not theories
Independent analyses leave no room for doubt:
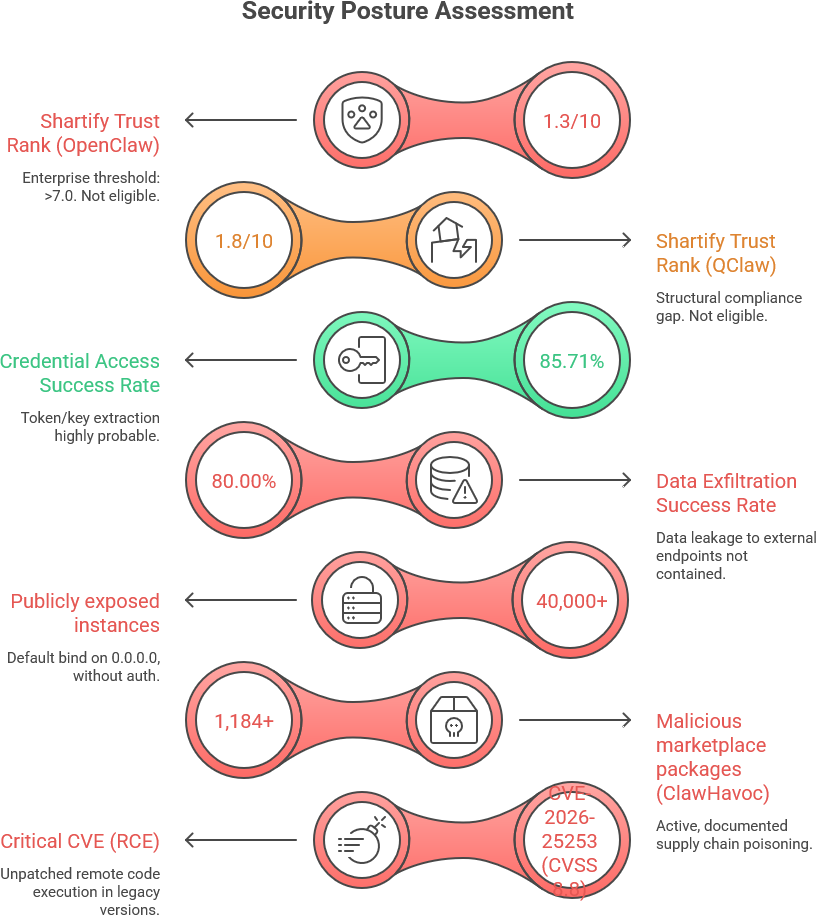
These aren't "potential risks." They are active attack vectors.
The Dutch Data Protection Authority (AP) has officially advised against using OpenClaw for sensitive data. Not out of paranoia. Based on technical evidence.
The compliance void: where do your data end up?
You connect an agent to your workflow. You give it access to emails, documents, invoices, databases, banking APIs. It "works for you". But who guarantees that:
- Data isn't being logged, analyzed, or aggregated?
- Traffic isn't routing through SG/US servers without residency clauses?
- There isn't a hidden telemetry module sending usage patterns back to the vendor?
- Your inputs aren't becoming training data for future commercial models?
The answer is simple: no one.
OpenClaw and QClaw do not publish Data Processing Agreements. They offer no certified mechanisms for right to erasure, data portability, or explicit GDPR consent. Data residency is non-configurable. Logs are local, not immutable, not exportable to enterprise SIEM.
In legal terms: you are transferring data to an unidentified processor, without contract, without audit, without guarantee.
If tomorrow that data is resold, profiled, or used to train a proprietary model, you have no legal basis to object. Because you never signed a DPA. Because "open-source" does not mean "privacy-by-design."
The future threat: latent backdoors and silent updates
The greatest risk isn't today. It's tomorrow.
When an agent already has your keys, it doesn't need to force anything. It just needs an update. A new core version. An "optimization module". A terms-of-service change.
The history of free infrastructure teaches us:
- Phase 1: Mass adoption with promises of automation
- Phase 2: Deep integration into personal/business workflows
- Phase 3: Silent introduction of telemetry, pattern collection, or data monetization
- Phase 4: Commercial pivot or acquisition. The data remains. You're left out.
QClaw, developed by Tencent, already routes data through Singapore/US servers. OpenClaw, born as a community project, sees its original creator move to OpenAI. The code remains. Governance changes. Privileges remain.
A modern trojan horse doesn't need to be malicious on day zero. It just needs to become so when it serves a purpose.
Direct and unfiltered: they aren't assistants. They're unverified privileged processes
If you're looking for pure automation, these tools work.
If you're looking for control, privacy, compliance, or assurance that your data won't become a tradable commodity, you're rolling dice with your infrastructure.
OpenClaw and QClaw are not certified. Not audited. No DPA offered. No data residency guarantees. They exhibit credential exfiltration success rates >85%. They have poisoned marketplaces. Default-exposed instances. Untracked patches. Non-existent support.This isn't theory. It's trust engineering applied to unsupervised processes.
What to do, without sugarcoating:
- ✅ Use only in isolated environments (air-gapped, dedicated VMs, no access to sensitive data)
- ✅ Never grant tokens, API keys, or admin accounts without external credential brokering
- ✅ Block internet access to the container/process unless strictly necessary
- ✅ Treat every update as a potential policy change: analyze the diff, don't trust the changelog
- ✅ For commercial use, GDPR compliance, or user data management: choose platforms with SOC 2, signed DPA, immutable audit trails, and legal SLAs
The free lunch ended years ago. Today, you pay with keys.
And when an agent enters legitimately, operates with your privileges, and no third party guarantees what it will do tomorrow... you aren't automating your life.
You're hosting an unverified process that already knows all your doors.
Shartify Trust Threshold: >7.0 for access to premium features, enterprise distribution, and data compliance. OpenClaw: 1.3. QClaw: 1.8. The gap isn't closed with promises. It's closed with audits, certifications, and binding contracts. Until then, trust is an unmitigated risk.
What's Your Reaction?